New Rule] Kubernetes Privileged Pod/Container Created · Issue #2031 · elastic/detection-rules · GitHub
GitHub - kubewarden/pod-privileged-policy: A Kubewarden Policy that limits the ability to create privileged containers
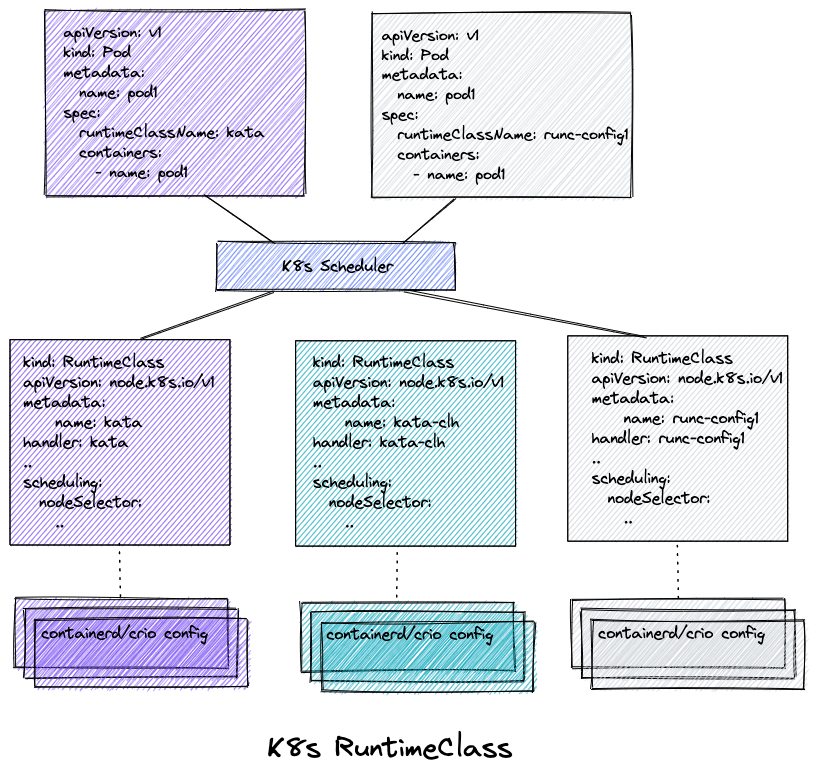
Enhancing Kubernetes Security with Kyverno, RuntimeClass, and Kata Containers | by Pradipta Banerjee | ITNEXT